How Human Risk Management (HRM) Tackles Cyber Threats by Addressing Human Vulnerabilities and Promoting Cybersecurity Sustainability
Human Vulnerabilities and the Rise of Human Risk Management (HRM)
Human behavior remains the primary entry point for cyber attackers. According to Verizon’s 2024 Data Breach Investigations Report, 68% of breaches in 2023 involved non-malicious human error—missteps such as sending sensitive information to the wrong recipient, misconfiguring access, or falling victim to social engineering. These human vulnerabilities have become one of the most persistent and systemic sources of cyber risk.
As a result, organizations are increasingly adopting Human Risk Management (HRM) as a critical evolution in cybersecurity practice.
What Is Human Risk Management (HRM)?
Human Risk Management (HRM) is the practice of identifying, assessing, and mitigating cybersecurity risks associated with human behavior in real time.
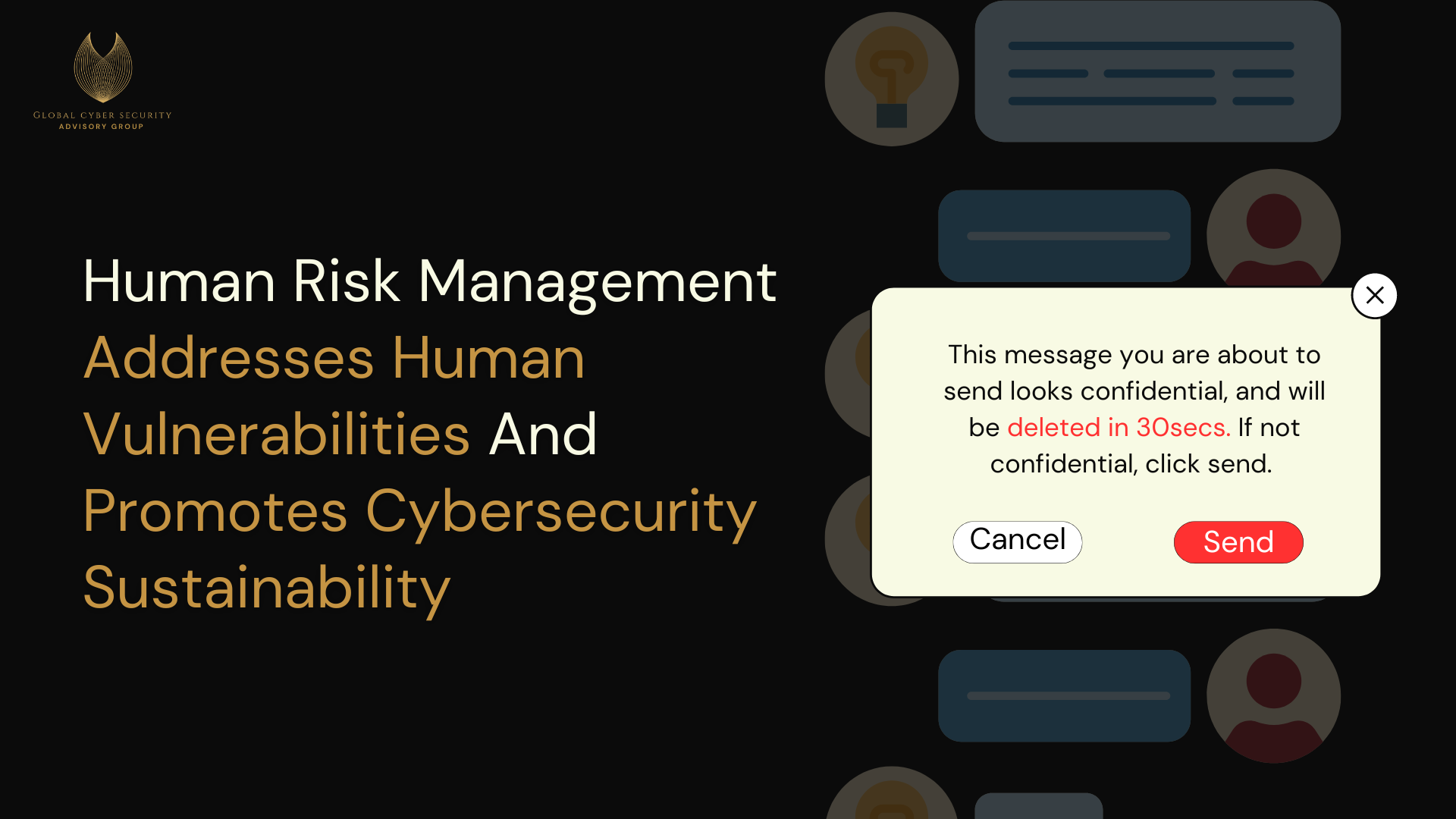
Rather than relying solely on periodic training or post-incident remediation, HRM uses context-aware, behavioral interventions—often referred to as nudges—to guide safer decision-making at the moment risk is introduced.
Examples include:
Alerts when sensitive data is about to be shared externally
Warnings prior to unsafe downloads or credential reuse
Time-bound prompts that allow users to reconsider potentially risky actions
These interventions are designed to interrupt risky behavior without disrupting productivity, helping individuals make better security decisions in context.
Why HRM Represents Cybersecurity Sustainability in Practice
Human Risk Management is a clear example of cybersecurity sustainability in action because it shifts security from a reactive, compliance-driven model to a long-term, adaptive, and human-centered approach.
Rather than treating people as the weakest link, HRM recognizes human behavior as:
Predictable
Influenced by cognitive bias and context
Responsive to timely guidance
By addressing the underlying behavioral drivers of risk, HRM reduces repeat incidents, limits unnecessary technical controls, and supports security practices that remain effective over time.
Benefits of Human Risk Management
Organizations that implement HRM experience measurable improvements across security, operations, and governance:
Enhanced Security Awareness
Targeted, real-time interventions reinforce learning far more effectively than one-time training. Employees gain practical understanding of secure behavior as they work.
Improved Risk Visibility
Continuous monitoring and automation provide clear insight into human-related risk patterns, enabling timely and proportionate responses.
Increased Operational Efficiency
By preventing errors before they escalate into incidents, HRM reduces disruption, downtime, and the need for costly remediation.
Stronger Compliance Posture
HRM supports regulatory expectations by demonstrating active management of human-related risks rather than passive policy enforcement.
Healthier Security Culture
Employees become participants in risk management rather than passive recipients of rules, fostering accountability and shared responsibility.
Cost Avoidance
Preventing incidents at the point of action reduces financial loss, reputational damage, and operational strain.
How HRM and Cybersecurity Sustainability Reinforce One Another
Cybersecurity sustainability and Human Risk Management share a common objective: building security practices that endure.
Cybersecurity sustainability focuses on long-term resilience across technological, social, and economic dimensions. HRM operationalizes that goal by ensuring that human behavior—often the most volatile risk factor—is addressed continuously and responsibly.
Together, they:
Promote adaptive, long-term security strategies
Reduce systemic fragility caused by repeated human error
Support efficient use of organizational resources
Protect not only systems, but stakeholders and communities
By minimizing preventable incidents, HRM also reduces the indirect environmental and operational costs associated with breach response, recovery, and system replacement—further reinforcing sustainability objectives.
Closing Perspective
Cybersecurity sustainability cannot be achieved through technology alone. As long as humans interact with systems, human risk must be governed, not ignored.
Human Risk Management provides a pragmatic, scalable way to address this reality. When integrated into a cybersecurity sustainability approach, HRM helps organizations build security practices that are not only effective today, but resilient, ethical, and sustainable over time.
In an era where human behavior is the primary attack surface, sustainable cybersecurity starts with understanding—and supporting—the human element.
Reference:
https://www.verizon.com/business/resources/reports/dbir/2024/summary-of-findings/
Cybersecurity Sustainability Practices for SMEs in the Face of Cyber Threats
Cybercrime is no longer a peripheral risk—it is a systemic economic threat. Cybersecurity Ventures projects global cybercrime damages will grow by approximately 15 percent annually, reaching $10.5 trillion USD by 2025, up from $3 trillion in 2015. This growth is driven by the expansion of cloud services, mobile platforms, Internet of Things (IoT) technologies, remote work environments, and increasingly sophisticated nation-state and organized criminal activity.
Small and medium-sized enterprises (SMEs) are disproportionately affected by this threat landscape. According to the World Economic Forum’s Global Cybersecurity Outlook 2024, SMEs outnumber large enterprises by more than two to one and are increasingly targeted precisely because of constrained resources and limited security maturity. Research consistently shows that a majority of SMEs do not recover after a major cyber incident, with many forced to close within months following a serious breach.
This risk extends far beyond individual businesses. SMEs employ nearly half of the private-sector workforce in many economies. When SMEs are disrupted at scale, the result is job loss, service interruption, and long-term economic instability.
Cybersecurity sustainability offers SMEs a path forward—not through expensive, enterprise-grade tooling, but through governance-aligned, resilient, and proportionate security strategies designed to endure over time.
Why Cybersecurity Sustainability Matters for SMEs
For SMEs, cybersecurity sustainability is not about perfection. It is about viability.
Cybersecurity sustainability enables SMEs to:
Protect financial stability over the long term
Reduce exposure to catastrophic disruption
Maintain continuity of operations during incidents
Align security investments with governance and capacity
Contribute to broader economic and societal resilience
Rather than relying on reactive, one-time security purchases, cybersecurity sustainability emphasizes systems that adapt, scale, and remain manageable as threats evolve.
Practical Cybersecurity Sustainability Strategies for SMEs
Cybersecurity sustainability for SMEs must be realistic, cost-conscious, and governance-driven. The following practices focus on resilience, efficiency, and continuity, not excess complexity.
1. Build Resilient, Adaptable Security Systems
SMEs should prioritize security architectures that can evolve over time—cloud-based services, managed security solutions, and modular controls that reduce dependence on constant hardware replacement and specialized staffing.
2. Align Cybersecurity with Business Governance
Security decisions should be tied to business risk, operational priorities, and leadership oversight. This ensures cybersecurity is treated as a continuity and risk-management function, not just an IT expense.
3. Reduce Operational and Resource Waste
Efficient system configuration, consolidated tooling, and streamlined security operations reduce unnecessary infrastructure, energy use, and maintenance costs—supporting both financial sustainability and operational clarity.
4. Focus on Incident Preparedness, Not Just Prevention
SMEs are more resilient when they prepare for disruption rather than assume it can be fully prevented. Sustainable incident response planning—including remote coordination, tabletop exercises, and clear escalation paths—reduces downtime, confusion, and financial loss.
5. Strengthen Human-Centered Security
Phishing, social engineering, and credential compromise remain the most common attack vectors against SMEs. Sustainable cybersecurity prioritizes ongoing awareness, simple controls, and repeatable training rather than one-time compliance exercises.
6. Measure What Matters
SMEs should track practical indicators such as:
System availability and recovery time
Frequency and impact of incidents
Cost of security operations relative to business size
Effectiveness of awareness and response processes
These metrics support continuous improvement without overwhelming limited resources.
Economic and Societal Impact
Cybersecurity sustainability for SMEs is not only about protecting individual businesses. It supports:
Workforce stability
Local and regional economic resilience
Trust in digital services
Continuity of supply chains and essential services
When SMEs fail due to cyber disruption, the effects ripple outward. Sustainable cybersecurity practices help prevent these cascading impacts by ensuring that small businesses remain operational, trustworthy, and capable of adapting to an evolving digital environment.
Closing Perspective
SMEs sit at the heart of the global economy—and increasingly, at the center of the cyber threat landscape. Traditional cybersecurity models that assume unlimited resources or specialized teams are neither realistic nor sustainable for this segment.
Cybersecurity sustainability offers SMEs a pragmatic alternative: security designed to last, aligned with governance capacity, economic reality, and long-term resilience.
By embedding cybersecurity sustainability into their operations, SMEs do more than protect themselves—they help safeguard jobs, communities, and economic stability in an increasingly digital world.
References:
https://cybersecurityventures.com/cybercrime-to-cost-the-world-9-trillion-annually-in-2024/
https://www3.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2024.pdf
Utilizing cybersecurity sustainability to safeguard community & ensure business continuity in times of war conflict
Cybersecurity Sustainability: An Answer for Conflict and War
Modern conflict no longer unfolds solely on physical battlefields. It now extends into digital systems that power economies, public services, communications, and civilian safety. As wars escalate, cyber operations increasingly target online businesses, public platforms, and critical digital infrastructure—creating cascading disruptions that affect not only institutions, but entire populations that depend on these systems to function.
In this environment, cybersecurity can no longer be treated as a narrow technical defense. Organizations must prepare for cyber conflict as a persistent condition, not a temporary threat. Cybersecurity Sustainability offers a governance-first approach to resilience—one that prioritizes continuity, accountability, and societal protection during instability.
Understanding Cyber Warfare in a Civilian Context
Cyber warfare involves the deliberate use of digital tactics to disrupt, degrade, or manipulate computer systems, networks, and information environments. These activities may be conducted by nation-states, proxy actors, criminal organizations, or ideological groups pursuing political, economic, or military objectives.
Unlike traditional warfare, cyber operations frequently blur the lines between military targets and civilian systems. Attacks often affect public utilities, healthcare platforms, financial services, transportation systems, media outlets, and emergency communication tools—placing civilians directly in the impact zone.
As digital dependence deepens, the consequences of cyber warfare extend beyond operational disruption. They undermine trust, spread disinformation, create fear, and destabilize societies already under strain. This reality demands a cybersecurity approach grounded in long-term resilience, governance, and public accountability.
Common Cyber Attacks During Conflict
Cyber warfare employs a range of tactics designed to exploit both technical vulnerabilities and human behavior. Common attack vectors include:
Malware Deployment
The use of malicious software to infiltrate systems, extract intelligence, manipulate data, or disrupt operations during conflict.Denial-of-Service (DoS and DDoS) Attacks
Flooding systems or networks with traffic to render services inaccessible, often targeting public-facing platforms or emergency services.Phishing and Social Engineering
Deceptive campaigns designed to trick individuals into revealing credentials or installing malware, frequently impersonating trusted authorities or officials.Ransomware Attacks
Encryption of critical systems—such as energy grids, transportation networks, or healthcare platforms—followed by ransom demands, creating widespread disruption during periods of instability.Cyber Espionage
Covert intelligence gathering targeting governments, militaries, corporations, and NGOs to gain strategic advantage or insight into adversary capabilities.Defacement and Information Manipulation
Altering websites or digital content to spread propaganda, intimidate populations, or undermine public confidence during conflict.
These attacks are not isolated technical incidents. They are strategic tools used to destabilize societies and exploit moments of vulnerability.
Case Study: Civilian Alert Systems Under Attack
A notable example of cyber conflict impacting civilians involved attacks on rocket and emergency alert applications. In one incident, a hacktivist group compromised an alert app by intercepting requests and injecting false warnings—including fabricated nuclear threats—into civilian communication channels.
In parallel, a malicious version of a legitimate alert application was distributed through deceptive websites. Disguised as trusted software, the application installed spyware that harvested sensitive user data and transmitted it to remote servers.
These attacks did more than compromise systems. They eroded trust in life-saving communication tools, amplified fear, and demonstrated how digital platforms meant to protect civilians can be weaponized during conflict.
Why Cybersecurity Sustainability Is the Necessary Response
In conflict environments, resilience is not defined by perfection—it is defined by the ability to endure, adapt, and recover without collapsing public trust or essential services.
Cybersecurity Sustainability provides that resilience by shifting focus from reactive defense to governance-led continuity. It emphasizes:
Long-term system reliability over short-term fixes
Clear accountability structures over fragmented vendor responsibility
Operational continuity for civilian-facing services
Risk governance that accounts for social, economic, and humanitarian impact
Rather than treating cybersecurity as an isolated technical function, cybersecurity sustainability integrates digital security into broader institutional responsibility—ensuring that systems remain functional, trustworthy, and aligned with societal needs during disruption.
What Must Change
In times of war and geopolitical instability, organizations must prioritize cybersecurity strategies that:
Embed governance, oversight, and decision-making authority at the leadership level
Protect both digital and operational systems that civilians depend on
Ensure continuity of essential services despite sustained attack conditions
Maintain trust, accuracy, and integrity in public communication channels
Reduce systemic fragility rather than relying on ad-hoc technical responses
Cybersecurity sustainability is not about adding environmental language to security programs. It is about building security that lasts under pressure, protects people as well as systems, and recognizes digital infrastructure as a public responsibility during conflict.
Closing Perspective
As cyber operations increasingly shape the outcomes of war, the question is no longer whether organizations will be targeted—but whether their systems are designed to endure.
Cybersecurity Sustainability offers a path forward. It strengthens institutional resilience, preserves public trust, and safeguards civilians who rely on digital systems in moments when failure carries real human consequences.
In an era where war is fought across networks as much as territory, cybersecurity sustainability is not optional. It is essential to protecting societies when stability is most fragile.
Benefits of Cybersecurity Sustainability
The Organizational Value of Cybersecurity Sustainability
Incorporating cybersecurity sustainability into organizational strategy delivers benefits that extend well beyond the protection of data and systems. When cybersecurity is treated as a long-term governance and resilience function, it becomes a driver of trust, operational efficiency, institutional credibility, and sustained value creation.
Organizations that adopt cybersecurity sustainability practices are better positioned to meet regulatory expectations, manage systemic risk, attract talent and investment, strengthen their brand, and remain resilient in an increasingly complex digital environment.
Key Benefits of Cybersecurity Sustainability
1. Enhanced Trust, Reputation, and Institutional Credibility
Organizations that demonstrate a commitment to responsible, governance-led cybersecurity strengthen trust with customers, partners, regulators, and the communities they serve. As expectations around ethical conduct, transparency, and accountability rise, cybersecurity sustainability signals that an organization takes its digital responsibilities seriously. This trust directly supports customer loyalty, partnership stability, and long-term reputation.
2. Stronger Compliance and Risk Management
Cybersecurity sustainability aligns security practices with evolving regulatory, legal, and oversight requirements. Rather than reacting to compliance pressures, organizations embed accountability and risk management into their operating model. This reduces exposure to regulatory penalties, litigation, and reputational damage while strengthening preparedness against cyber incidents and systemic disruptions.
3. Long-Term Cost Efficiency
Sustainability-driven cybersecurity emphasizes efficiency, proportionality, and lifecycle planning. Investments in scalable architectures, cloud optimization, and resource-efficient infrastructure reduce operational waste and avoid costly, reactive remediation. Over time, this approach lowers total cost of ownership and prevents the financial volatility associated with repeated crisis response.
4. Talent Attraction and Retention
Organizations with a clear commitment to sustainability—including cybersecurity sustainability—are increasingly attractive to skilled professionals who value purpose, ethics, and long-term impact. A governance-first security posture signals organizational maturity, supports workforce stability, and helps retain talent critical to managing complex digital risk environments.
5. Increased Investment and Funding Opportunities
Investors and funding bodies are placing greater emphasis on environmental, social, and governance (ESG) performance. Demonstrating cybersecurity sustainability strengthens an organization’s ESG profile by showing that digital risk is being managed responsibly and strategically. This alignment can unlock access to capital, partnerships, and development funding.
6. Innovation and Competitive Advantage
Cybersecurity sustainability encourages innovation by shifting organizations away from short-term, compliance-only thinking toward resilient, future-ready design. Organizations that embed sustainability into their cybersecurity strategy are better positioned to lead in their markets, differentiate themselves from competitors, and adapt to emerging technologies and threat landscapes.
7. Long-Term Organizational Resilience
At its core, cybersecurity sustainability is about endurance. By aligning cybersecurity with governance, operational reality, and societal impact, organizations build systems capable of evolving alongside technological change. This resilience supports continuity of operations, protects institutional mission, and reduces the likelihood of cascading failures across digital, physical, and social systems.
Integrating Cybersecurity Sustainability in Practice
To realize these benefits, organizations must move beyond isolated technical controls and integrate cybersecurity sustainability into enterprise decision-making. This includes:
Conducting comprehensive, risk-informed assessments
Aligning cybersecurity strategy with broader sustainability and governance objectives
Investing in scalable, sustainable technologies
Continuously evaluating and adapting practices in line with evolving global standards
Cybersecurity sustainability is not a one-time initiative—it is an ongoing commitment to responsible digital stewardship.
Closing Perspective
As digital systems become foundational to economic activity, public services, and social trust, organizations can no longer afford cybersecurity strategies that prioritize short-term protection over long-term impact.
Cybersecurity sustainability offers a pathway to security that lasts—technically, institutionally, and socially. By embedding governance, accountability, and resilience into cybersecurity practice, organizations strengthen not only their defenses, but their capacity to thrive in an increasingly interconnected world.
Understanding Cybersecurity Sustainability
It all begins with an idea.
Sustainable Cybersecurity vs Cybersecurity Sustainability
Although often used interchangeably, sustainable cybersecurity and cybersecurity sustainability represent two distinct — and importantly different — approaches to digital security.
Sustainable Cybersecurity
Sustainable cybersecurity generally refers to the ability to design, implement, and maintain cybersecurity measures that endure over time.
This approach focuses on:
Building resilient and adaptable security architectures
Ensuring tools, policies, and controls can be maintained and updated as threats evolve
Avoiding brittle, one-off solutions that degrade under operational strain
In practice, sustainable cybersecurity emphasizes the longevity and effectiveness of security controls themselves. It asks:
Can this security posture be sustained operationally, financially, and technically over time?
This framing is largely internal and technical, centered on infrastructure durability and defensive capability.
Cybersecurity Sustainability
Cybersecurity sustainability, by contrast, situates cybersecurity within a broader governance, societal, and systems context.
Rather than focusing solely on whether security tools endure, cybersecurity sustainability examines:
How cybersecurity decisions affect institutions, communities, and public trust
Whether security practices align with ethical, social, environmental, and economic realities
How governance structures ensure accountability, equity, and long-term resilience
Cybersecurity sustainability recognizes that digital security does not operate in isolation. Security failures ripple outward — impacting civil liberties, economic stability, service delivery, and human safety.
In this framing, cybersecurity becomes:
A governance issue, not just a technical one
A risk management function embedded in enterprise and societal systems
A contributor to — or detractor from — sustainable development outcomes
In essence:
Sustainable cybersecurity asks whether security controls last
Cybersecurity sustainability asks whether security decisions hold up responsibly over time — for people, institutions, and society
Why Cybersecurity Sustainability Matters
In today’s interconnected digital environment, cybersecurity sustainability is increasingly critical across sectors including:
Humanitarian and development organizations
Energy and utilities
Water and wastewater systems
Financial services
Healthcare
Transportation systems
Education and academia
Hospitality and service industries
These sectors face interdependent digital, physical, and operational risks that cannot be addressed through technology alone.
Cybersecurity sustainability provides a framework for addressing these challenges through a set of integrated, governance-driven considerations:
Core Dimensions of Cybersecurity Sustainability
Ongoing and Proactive Effort
Cybersecurity is not static. Sustainable approaches require continuous assessment, improvement, and adaptation across digital, physical, and operational domains.
Comprehensive Security
Effective security extends beyond networks and data to include physical infrastructure, operational procedures, and human behavior.
Integration of Digital and Physical Realms
Servers, devices, facilities, communications, and the people who operate them must be secured as a unified system.
Long-Term Resilience
Systems must withstand disruption — cyber or otherwise — and recover quickly without cascading failure.
Alignment with Broader Sustainability Goals
Security strategies should support environmental responsibility, social equity, and economic stability rather than undermine them.
Environmental Responsibility
Consideration of energy consumption, infrastructure efficiency, and the environmental impact of security operations.
Social Equity
Ensuring equitable access to secure digital services and protections, particularly for marginalized or under-resourced communities.
Economic Viability
Balancing cost, risk reduction, and long-term value to avoid unsustainable security investments or false economies.
Operational Security Integration
Embedding security into everyday processes to prevent leakage, misuse, or governance gaps throughout the lifecycle of operations.
Enterprise Context: SMEs and Large Organizations
Cybersecurity sustainability also accounts for organizational scale and context.
Small and medium enterprises (SMEs) often face resource constraints, limited expertise, and compliance burdens that require proportionate, governance-aligned solutions.
Large enterprises contend with complex IT ecosystems, global operations, regulatory fragmentation, and the protection of high-value intellectual property.
A sustainability-driven approach enables both to prioritize risk intelligently, align security with governance capacity, and avoid reactive or unsustainable security models.
Closing Perspective
As digital systems increasingly underpin economic activity, public services, and social interaction, cybersecurity sustainability is no longer optional.
It provides a path toward security that lasts — not only technically, but institutionally and socially.
By prioritizing governance, accountability, and long-term impact, cybersecurity sustainability strengthens not just systems and data, but the societal foundations that depend on them.
Bridging the Digital Divide: The Journey of Global Cyber Security Advisory Group and its Quest for Social Equity
It all begins with an idea.
Introduction
Welcome to the first official blog post from Global Cyber Security Advisory Group.
Over the course of my career in cybersecurity, one truth became increasingly clear: the challenge is not simply a lack of technical education or tools. At its core, cybersecurity is about safeguarding civil liberties, institutional trust, and human dignity in an increasingly digital world.
Global Cyber Security Advisory Group exists to address that reality. Our mission is grounded in the belief that access to effective, responsible cybersecurity is not a luxury—it is a prerequisite for resilient communities, functioning institutions, and sustainable societies. When digital systems fail, the consequences extend far beyond data. They affect livelihoods, public safety, and democratic participation.
As a social enterprise operating within the broader ecosystem of the Protect Us Kids Foundation, Global Cyber Security Advisory Group brings a governance-first approach to cybersecurity—one that prioritizes accountability, long-term resilience, and equitable access, particularly for rural and under-resourced communities worldwide.
Mission and Vision
Our vision is bold and clear: Global Cyber Security (“GCS”) Advisory Group is on a path to become a global leader in cybersecurity sustainability. We are dedicated to highlighting the vital link between cybersecurity and societal challenges. Our focus? To use digital security as a catalyst for social change and equality.
Strategy and Approach
Global Cyber Security Advisory Group operates as a governance-led consortium.
Rather than delivering isolated or one-off technical services, we serve as a central coordination and oversight entity—bringing together vetted member organizations with specialized capabilities to execute cybersecurity and digital risk initiatives responsibly and at scale.
Our approach is intentional:
Centralized governance and accountability, guided by the Cybersecurity Sustainability Framework™
Distributed execution, delivered through consortium member expertise
Alignment with regulatory, operational, and regional realities
Long-term resilience over short-term remediation
This model allows us to support complex, multi-jurisdictional environments while reducing vendor risk and ensuring consistent governance across engagements.
Expanding Cybersecurity Access and Awareness
Global Cyber Security Advisory Group works to extend cybersecurity access to communities and institutions historically excluded from advanced digital security resources.
Governance-aligned services designed for real-world operational contexts
Risk-informed education and awareness initiatives that strengthen decision-making at the community and organizational level
Cybersecurity sustainability depends not only on tools, but on understanding, accountability, and trust.
Workforce Capacity and Opportunity
A core pillar of our work is developing human capital.
Through partnerships, apprenticeships, and internships, we help create pathways into cybersecurity and digital risk careers—particularly for individuals in rural and under-resourced regions. These initiatives are designed to build local capacity, reduce dependency on external expertise, and foster long-term resilience within communities.
Graduates often continue into roles within the consortium ecosystem or with aligned partners, supporting a sustainable cycle of growth and opportunity.
Sustainable Model
Global Cyber Security Advisory Group operates as a social enterprise.
Proceeds from our services are reinvested to support mission-aligned initiatives, including the work of the Protect Us Kids Foundation. This structure enables us to deliver professional, accountable cybersecurity services while reinforcing long-term community development and online child protection efforts.
Sustainability, for us, is both operational and ethical.
Global Recognition and Influence
Our model is increasingly recognized as a viable blueprint for integrating cybersecurity, governance, and social impact.
We collaborate with public, private, academic, and nonprofit partners to advance responsible cybersecurity practices globally—not for recognition alone, but to strengthen collective capacity and shared accountability in an interconnected digital ecosystem.
Challenges and Adaptations
Like any organization working at the intersection of governance, technology, and equity, we have faced challenges—from resource constraints to early skepticism. These realities have shaped our approach, reinforcing the importance of partnerships, adaptability, and disciplined governance.
Resilience is not theoretical for us; it is operational.
Looking Forward
Global Cyber Security Advisory Group is continuing to expand its reach, deepen its consortium capabilities, and refine its methodologies. As digital risk grows more complex, so too must the structures designed to manage it.
We remain focused on building cybersecurity models that endure—models that protect systems, empower people, and strengthen institutions over time.
Our Commitment
Cybersecurity is no longer solely a technical function. It is a governance issue. A societal issue. A human issue.
At Global Cyber Security Advisory Group, we are committed to advancing cybersecurity sustainability as a means of strengthening digital public infrastructure, reducing systemic risk, and supporting more equitable outcomes worldwide.
In doing so, we are not only securing systems—we are investing in communities, trust, and the future.
Thank you for being part of this journey.
Veda T. Woods, CEO & Founder